This post is about PKCE [RFC7636], a protection mechanism for OAuth and OpenIDConnect designed for public clients to detect the authorization
code interception attack.
At the beginning of our research, we wrongly believed that PKCE protects mobile and native apps from
the so called „App Impersonation“ attacks. Considering our ideas
and after a short discussion with the authors of the PKCE
specification, we found out that PKCE does not address this issue.
In other words, the
protection of PKCE can be bypassed on public clients (mobile and
native apps) by using a maliciously acting app.
OAuth Code Flow
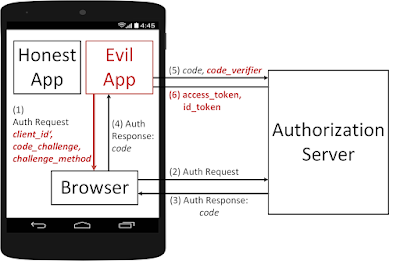
In Figure 1, we briefly introduce how the OAuth flow works on mobile apps and show show the reason why we do need PKCE.
In our example the user has two apps installed on the mobile phone: an Honest App and an Evil App. We assume that the Evil App is able to register the same handler as the Honest App and thus intercept messages sent to the Honest App. If you are more interested in this issue, you can find more information here [1].
 |
| Figure 1: An example of the "authorization code interception" attack on mobile devices. |
Step 1: A user starts the Honest App and initiates the
authentication via OpenID Connect or the authorization via OAuth.
Consequentially, the Honest App generates an Auth Request containing
the OpenID Connect/OAuth parameters: client_id, state,
redirect_uri, scope, authorization_grant, nonce, ….
Step 2: The Browser is called and the Auth Request is sent to the Authorization Server (usually Facebook, Google, …).
- The Honest App could use a Web View browser. However, the current specification clearly advice to use the operating system's default browser and avoid the usage of Web Views [2]. In addition, Google does not allow the usage of Web View browser since August 2016 [3].
Step 4: Now, the browser calls the Honest App registered handler. However, the Evil App is registered on this handler too and receives the code.
Step 5: The Evil App sends the stolen code to the Authorization Server and receives the corresponding access_token in step 6. Now, the Evil App can access the authorized ressources.
- Optionally, in step 5 the App can authenticate on the Authorization Server via client_id, client_secret. Since, Apps are public clients they do not have any protection mechanisms regarding the storage of this information. Thus, an attacker can easy get this information and add it to the Evil App.
Proof Key for Code Exchange - PKCE (RFC 7636)
Now, let‘s see how PKCE does prevent the attack. The basic idea
of PKCE is to bind the Auth Request in Step 1 to the code redemption in Step 5.
In other words, only the app generated the Auth Request is able to
redeem the generated code.
Step 2: The Authorization Server receives the Auth Request and binds the code to the received code_challenge and challenge_method.
 |
| Figure 2: PKCE - RFC 7636 |
Step 1: The Auth Request is generated as previosly described. Additionally, two parameters are added:
- The Honest App generates a random string called code_verifier
- The Honest App computes the code_challenge=SHA-256(code_verifier)
- The Honest App specifies the challenge_method=SHA256
Step 2: The Authorization Server receives the Auth Request and binds the code to the received code_challenge and challenge_method.
- Later in Step 5, the Authorzation Server expects to receive the code_verifier. By comparing the SHA-256(code_verifier) value with the recieved code_challenge, the Authorization Server verifies that the sender of the Auth Request ist the same as the sender of the code.
Step 3-4: The code leaks again to the Evil App.
Step 5: Now, Evil App must send the code_verifier together with the code. Unfortunatelly, the App does not have it and is not able to compute it. Thus, it cannot redeem the code.
PKCE Bypass via App Impersonation
Again, PKCE binds
the Auth Request to the code
redemption.
The
question rises, if an Evil App can build its own Auth Request with
its own code_verifier, code_challenge and challenge_method.
The short answer is – yes, it can.
 |
| Figure 3: Bypassing PKCE via the App Impersonation attack |
Step 1: The Evil App generates an Auth Request. The Auth Request contains the client_id and redirect_uri of the Honest App. Thus, the User and the Authorization Server cannot recognize that the Evil App initiates this request.
Step 2-4: These steps do not deviate from the previous description in Figure 2.
Step 5: In Step 5 the Evil App sends the code_verifier used for the computation of the code_challenge. Thus, the stolen code can be successfully redeemed and the Evil App receives the access_token and id_token.
OAuth 2.0 for Native Apps
The attack cannot be prevented by PKCE. However, the IETF working group is currently working on a Draft describing recommendations for using OAuth 2.0 for native apps.
References
Vladislav Mladenov
Christian Mainka (@CheariX)
Christian Mainka (@CheariX)



